How to Protect Your Website Against Spammers and Hackers
I recently suffered some big attacks on a WordPress website that I manage, which forced us to really beef up our security measures. For anyone running their own websites, security is a really big concern. Below are the steps I used to stop the attack and protect it for next time. Fortunately, nothing bad happened as security was already set up at a decent level. This attack was more of a nuisance, but it could have ended up being much worse.
Below is a guide to protecting your WordPress site, based on the techniques I have deployed to protect mine.
Why Should I Use WordPress?
WordPress is great for many reasons: it’s simple; easy to use; has plugins for just about anything; and of course, it’s free. Being open source has allowed it to be all of these things and has seen it become the most popular Content Management System on the internet.
Why Attack WordPress?
However, the open source nature and popularity also make it an attractive target for hackers. There are many reasons why a nefarious actor may wish to attack a WordPress site, but if you are under attack take some comfort in knowing that it is almost certainly nothing personal against you.
What Does a WordPress Attack Look Like?
An attack on WordPress can take on many forms, but these are typical symptoms to look at:
- Lots of spam comments, or email notifications asking you to moderate comments
- New content appearing on your site (in the form of blog posts or pages)
- Files being uploaded to other areas of your site without you knowing
- Google or another browser or search engine flagging your site as dangerous or malicious
- Your website loading a lot slower than usual with no other obvious reason
- Your web hosting being suspended or terminated
- Your website showing an error like 503 server error
These may not always be because of an attack and there are also other symptoms, but if these things happen it should be one of the things you look for.
Let’s look at how to block the most common types of attack.
How to Stop Spam Comments on WordPress
Spam is one of the most common attacks to a WordPress site. Typically, spam comments are left by people hoping that they will be able to get a link back to their own website. While there may not be anything wrong with this in principle, the problem is that these links are typically to low quality, illegal, or dangerous websites.
Require Moderation of Comments in WordPress
There are some really simple ways to stop this type of attack. Firstly, requiring moderation of comments before they are approved can help to stop spam. However, this doesn’t always seem to dissuade the spammers, who are typically using software to automate their spamming. If you haven’t already enabled this, you may want to try it first. But you’ll likely need to try another step.
Use Akismet to Stop Spam Comments on Your WordPress Site
Akismet is an incredibly powerful WordPress plugin that has one purpose, the block spam comments from your website. It is now 15 years old and claims to block 7.5 million pieces of spam every hour! It has a free version for people who are not using their website for commercial purposes, and then a paid version that is £4 per website, per month.
It works by combining intelligence from all of the websites that use the plugin. This has helped to create a huge database of spam comments, allowing the plugin to silently delete the rubbish from your WordPress site before you even see it.
Fortunately, Akismet comes preinstalled with WordPress, you just need to activate it and then setup a subscription.
Turn Off Comments in WordPress
If all else has failed, you can just turn off comments altogether. This will work great for anyone who is not running a blog that wants or needs engagement, so business websites that are using their blog to showcase their products and no much else.
How to Stop Unauthorised Access to Your WordPress Site
WordPress has some really handy features for integrating into other software and for letting you manage your site from your phone. However, if you’re not planning to use these features, or are struggling with attacks, then here is a way to stop one of the most targeted parts of WordPress.
What is xmlrpc.php in WordPress?
This system is called XML – RPC (XML Remote Procedure Call), and WordPress handles it through a file called xmlrpc.php. XML-RPC allows two applications to talk to each other, and in WordPress it allows you to control it from other apps. This tool is so powerful it can also be used for attacking your WordPress site.
What does an XML-RPC Attack Look Like in WordPress?
An XML-RPC attack can be used to brute force the administrator user accounts. The protocol can be used to send thousands of attacks in a very short period of time. This is much more efficient for them than trying to login using the normal WordPress login page (wp-login.php), as they are able to try hundreds of different passwords with just a handful of HTTP requests.
This will not show up as much in your connection logs but will put a lot of strain on your database and cause it to intermittently show error messages. As well as your site running slowly, you may see these errors as a result of an XML-RPC attack.
- “Error establishing database connection” when trying to access the site (permanent or intermittent).
- “Out of memory” appearing in the web console.
- “Cannot open the file no such file/directory” appearing in the web server’s error log.
- “POST /xmlrpc.php HTTP/1.0” appearing in the web server’s error log.
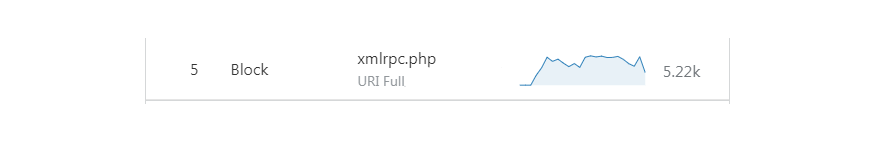
During the peak of an attack that targeted one of my sites, XML-RPC attacks were hitting more than 5,000 attempts in a single day. 24 hours after implementing some of the security measures listed below, this was the number of attacks the software had blocked.
What Are the Other Risks of XML-RPC Attacks?
Obviously, your site going offline is going to cause you a lot of headaches and perhaps some lost revenue. However, if you’re using a service like Amazon Web Services to host your site, you will also be paying for resources that you really don’t want. Therefore, it’s important to get an XML-RPC attack stopped as quickly as possible.
How to Disable xmlrpc.php in WordPress
The XML-RPC feature can be disabled directly in WordPress. However, you may wish to go one step further though, and completely block access to the xmlrpc.php file. This will be most effective if you don’t use any software that makes use of the protocol, but you may even decide that disabling it in the short term may help to make the attack go away quicker.
You can disable access to xmlrpc.php on your own server by using the .htaccess file. Simply paste in the following:
# Block access to the xmlrpc.php file in WordPress
<Files xmlrpc.php>
order deny,allow
deny from all
</Files>
# END xmlrpc.php blocking
You can go one step further though. By using Cloudflare, you can completely stop these requests from hitting your server, protecting you from the load on the server. To do this, you first need a Cloudflare account. If you don’t have one, this guide will explain more.
Once you’re up and running with Cloudflare, you can block access to anyone trying to use the xmlrpc.php file by clicking:
Firewall > Firewall Rules > Create a Firewall rule
When you’re here, type in a “Rule name”, then select “URI Full” in “Field”, “equals” and type this into “Value”:
https://YOURDOMAIN.COM/xmlrpc.php (where YOURDOMAIN.com is replaced with your own domain name)
Click “Or” and select the same values and then enter this into “Value”
This blocks the HTTP and HTTPS versions of the request. Be careful to make sure that you use (or don’t use) www. In your domain name, depending on whether or not your WordPress site uses it.
Then click “Deploy”.
Verify this has worked by trying to visit the page yourself. If it gives you a message saying: “Error 1020 – Access Denied”, then you know it has worked.
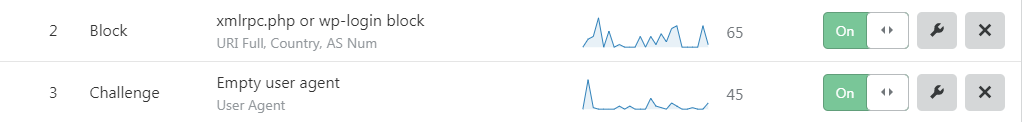
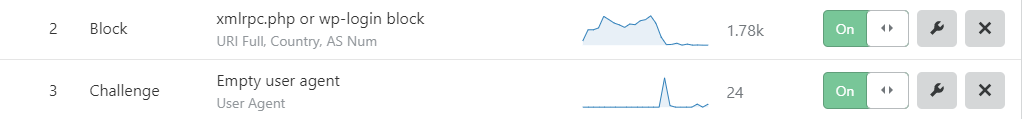
Form the Firewall Rules page you can then see how many attacks your rule has blocked in the last 24 hours. As you can see below, the xmlrpc.php file can be a very popular way of attacking a WordPress installation.
How to Block Attempts to Hack Your WordPress Site Through WP-Login.php
The other way to log in to a WordPress site is through the normal login page that you would use. Because WordPress is such a popular CMS, it is easy for hackers to find the login page. One of the easiest tricks to stop this is to move the login page to somewhere else, meaning anyone trying to access wp-login.php will be shown a 404 error.
You can do this manually, but its cleaner and easier to do it with a plugin. One of the best and highest rated plugins to use is called WPS Hide Login. Once installed and activated, you can change the login URL quickly from the XXXX page.
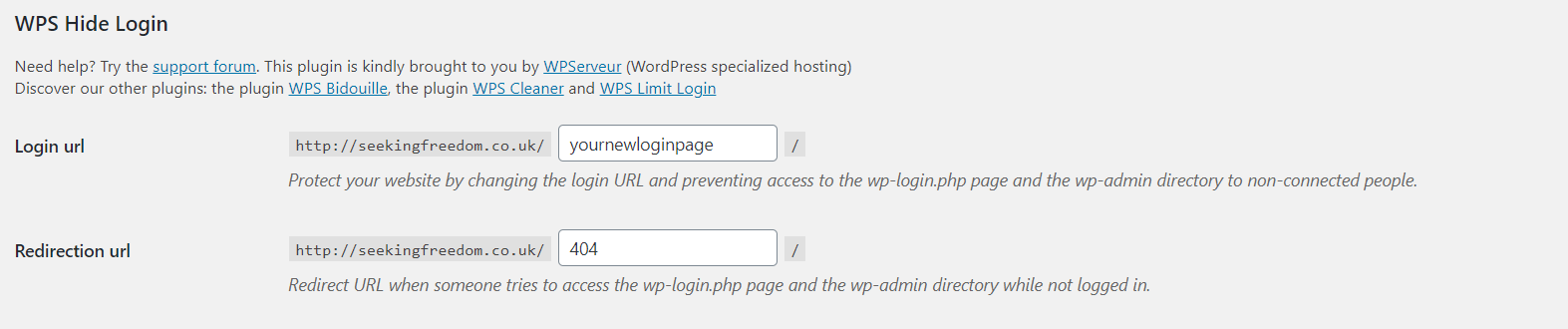
Just remember to save the new URL. If you don’t you will find it very difficult to log in again.
How to Block Access to WP-Login.php for WordPress
One you have changed the URL to log in, you can use the same approach in Cloudflare to block access to the old wp-login.php. Once you’ve applied the test, be sure to test that it’s working by trying to visit https://YOURDOMAIN.com/wp-login.php and http://YOURDOMAIN.com/wp-login.php. If you get the 1020 Access Denied error, then you’re all set.
Why You Should Never Have “admin” as Your Username
From monitoring the attacks on a WordPress site I manage, I noticed that there seemed to be a list of favourite generic accounts that hackers were trying to exploit. None of these accounts existed on this website, so they were not able to get in. However, if you have any of these usernames, you should consider created a new account and removing the old one.
Make Sure You Have a Strong Password
You will get told all the time that you must have a secure password that cannot be easily guessed. Most websites now require your password to be at least 8 characters long and contain numbers, uppercase letters, lowercase letters, and symbols. You should definitely make sure this is also the case for WordPress.
Also remember never to re-use your passwords elsewhere. If you struggle to remember lots of passwords, consider using a password manager like LastPass. This is a service that I have been using for well over 5 years, and I don’t know what I would do without it.
Also register yourself on HaveIBeenPwned.com. This will tell you if any of your usernames, email address, or passwords have ever been (or are in the future) compromised in a data leak.
How to Use Two-Factor Security on WordPress
Another great way of protecting your WordPress user accounts from being hacked is to use two-factor authentication (2FCA). You will find two-factor security on many services now, including sites like Facebook, Twitter, Google, and Amazon.
There are many plugins you can use to protect your WordPress website with two-factor authentication, however one of the best options is to install WordFence.
WordFence all-round security plugin for WordPress, featuring a firewall, login protection, and more. Once you install and activate it WordFence, you can turn on two-factor authentication in just a few easy steps.
Advanced users can also use WordFence to block login attempts from people who guess incorrect usernames or fail to reset the password of too many accounts.
How to Close Security Loopholes in WordPress
Software can always end up with bugs and weak points that can be exploited by hackers. That is why your computer will regularly ask you to run updates. WordPress is no different.
So, to keep your WordPress website protected from hackers you should always run the updates when it recommends it. These updates will provide security patches that will close known loopholes, as well as provide performance improvements and new features. You should do this for WordPress itself, as well as themes and plugins.
Other Tips for Securing Your WordPress Site
There are always more things you can do to keep yourself protected. Once you reach a certain level you will likely need to hire someone to take care of things for you, particularly things at a server level outside of WordPress.
This is what I have done, although I can make changes directly to the server, I would rather pay for someone who is an expert to do it. The risk can be too high if I make a mistake.
However, there are also some more tweaks you can make to WordPress to increase security, these include:
- Remove any plugins that you don’t use
- Install JetPack – this is slightly controversial as it can be a bit bloaty, however it does include some useful security features
- Don’t use pirated (nulled) themes or plugins
- Block access to wp-config.php using the same method listed above
- Disable file editing of files by adding define(‘DISALLOW_FILE_EDIT’, true); to your wp-config.php file
- Use encryption by installing an SSL certificate
- Change the database prefix (WordPress calls everything wp_ by default) – it’s easier to do this when you first set up WordPress, but it can be done afterwards with plugins like WP-DBManager
- Regularly backup your site so you can revert back in the event of an attack
- Remove your WordPress version number either through code, or with a plugin
Success in Blocking WordPress Attacks
After implementing these steps, I managed to reduce the amount of attempts at attacking the site down to just a few dozen each day. This happened very quickly too, as the nefarious people quickly moved on to someone else.
48 hours out, attacks via XML-RPC or wp-login have gone from more than 5,000 to just over 3,000.
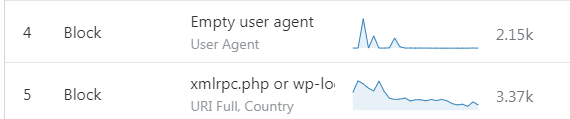
72 hours out, attacks are less than 2,000. As you can see, I have refined the rules slightly based on logs in Cloudflare.
A few days later and most attempts have stopped, people have decided not to waste their time.